The role of a network engineer is very critical in any organization and it is important to have sound knowledge of networking concepts while applying for a role. Common Interview Questions for Network Engineers is to help networking candidates focus on typical screening questions and develop thorough understanding so as to ace an interview as well as handle issues on job.
Note that this is a guest post by Ahmed Zeeshan, Senior IP MPLS Engineer and we are extremely thankful to him for sharing his experience and knowledge on our blog in order to help networking professionals.
Common Interview Questions for Network Engineers
1. Difference between of STP and RSTP
Both are used to avoid L2 Loops however there are certain differences in terms of convergence timers and thus number of states in these protocols.
Convergence Timers:
- STP (802.1d): 50 ms
- RSTP (802.1w): 6 ms
STP States – Disabled, Blocking, Listening, Learning & Forwarding
RTSP States – Discarding (replaces disabled, blocking and listening), Learning & Forwarding
2. Difference between Root guard, BPDU guard and Loop guard
Root Guard: It prevents a port from becoming the root port.
BPDU Guard: State of the port changes to Error-disable in case a BPDU is received.
Loop Guard: It prevents a port to transit from blocked state to listening state after max age timer gets expired.
3. Explain the phenomenon of Q-in-Q
Using Q-in-Q tunneling, providers can segregate or bundle customer traffic into fewer VLANs or different VLANs by adding another layer of 802.1Q tags. Q-in-Q tunneling is useful when customers have overlapping VLAN IDs, because the customer’s 802.1Q (dot1Q) VLAN tags are prepended by the service VLAN (S-VLAN) tag.
In Q-in-Q tunneling, as a packet travels from a customer VLAN (C-VLAN) to a service provider’s VLAN, a customer-specific 802.1Q tag is added to the packet. This additional tag is used to segregate traffic into service-provider-defined service VLANs (S-VLANs). The original customer 802.1Q tag of the packet remains and is transmitted transparently, passing through the service provider’s network. As the packet leaves the S-VLAN in the downstream direction, the extra 802.1Q tag is removed.[1]
4. Difference between Kompella and Martini L2 VPNs
- Martini Draft uses LDP for signaling the connection whereas Kompella uses BGP.
- Martini Drafts are a bit simpler to implement/configure and you can use targeted LDP.
- Kompella needs more configuration since you need configuring routing instances and enabling family L2VPN signaling under the BGP configuration which definitely leads to BGP session tear down and establish again.[2]
5. Difference between LACP and VRRP
VRRP: VRRP (Virtual Router Redundancy Protocol) is used to provide redundancy at router level and make sure that network remains intact even if one of the router goes down.
In VRRP, a virtual router is created, this virtual router is made up of a single router acting as virtual router master and there are multiple routers acting as virtual router backup. The virtual IP address of the virtual router is then configured on LAN clients as their default gateway. IP address on all VRRP Master /Backup routers and VRRP clients always belong to the same subnet.
LACP: LACP is providing redundandancy of one link on a router. LACP is part of the IEEE specification 802.3ad and it allows you to bundle several physical ports to form a single logical channel.
In LACP, the logical link remains UP even if one of the link goes down. As per network design and in order to address congestion issues ( and force switching to another interface/router) an LACP Link can be made down even if one or more links are UP in that bundle (using minimum links command).
6. Different LACP Modes
LACP packets are exchanged between ports in these modes:
- Active: Places a port into an active negotiating state, in which the port initiates negotiations with remote ports by sending LACP packets.
- Passive: Places a port into a passive negotiating state, in which the port responds to LACP packets it receives but does not initiate LACP negotiation. In this mode, the port channel group attaches the interface to the bundle.[3]
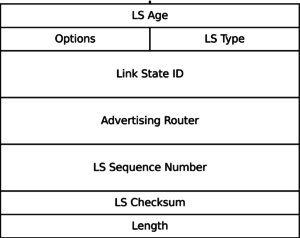
7. Difference between OSPF LSA types 3, 4 & 5
Type 3 LSAs (Summary LSA) are generated by Area Border Routers (ABR) to summarize its directly connected area, and advertise inter-area router information to other this ABRs (with the help of summary prefix).
Type 4 LSAs advertise the presence of an ASBR to other areas. It is worth noticing that while type 4 LSAs are used by ABRs to advertise the ASBR route through their areas, it will not be used by the ASBR itself within its local area (Area 1), ASBR uses LSA Type 1 to inform its neighbors (R2 in this case) within its network.
Type 5 LSAs are generated by the ASBR to advertise external redistributed routes into the OSPF’s AS. These external redistributed route/prefix are seen as O E1 or E2 entries in other OSPF routers routing tables.[4]
8. Difference between Stub Area and Totally Stub Area
Stub Area: LSA‐4, LSA‐5 is not advertised into a Stub area
Totally Stub Area (Totally Stub): No LSA‐3, LSA‐4 and LSA‐5
Not So Stubby Area (NSSA): A stub area containing an ASBR, type 5 LSAs are converted to type 7 within the area.
9. The most common reason of OSPF stuck in Exstart/Exchange state?
MTU mismatch is the most common reason.
10. Reasons for OSPF stuck in INIT state
Reasons: Layer-2 problems, ping and trace or access-list blocking the multicast 224.0.0.5 address.
11. Difference between CSNP and PSNP in IS-IS Protocol
Complete Sequence Numbers PDU (CSNP) and Partial Sequence Numbers PDU (PSNP) packets are used to synchronize link-state databases. CSNP packets are very similar in their function to OSPF Database Description Packets.
The purpose of CSNP packets is to advertise a complete list of LSPs in the sender’s link-state database. Receivers of CSNP packets can compare their link-state database contents to the list of LSPs in the CSNP and perform appropriate action – flood a newer or missing LSP if they have one, or request an LSP if they find it missing in their own database.
PSNP packets are functionally similar to OSPF Link State Request and Link State Acknowledgment packets. Using PSNP, a router can either request a particular LSP or acknowledge its arrival.
A single PSNP can request or acknowledge multiple LSPs. As a PSNP is intended to request or acknowledge individual LSPs by their LSPIDs, there are no Start or End LSPID fields present in PSNPs.
CSNP and PSNP packets are used to facilitate link-state database synchronization. CSNP packets contain a list of all LSPs in a sender’s link-state database, allowing the recipient to compare this list to the index of its own link-state database. PSNP packets are used to request an LSP or acknowledge its successful arrival.[5]
12. Hello and Hold Timers in OSPF, IS-IS and EIGRP
EIGRP: By default, EIGRP sends Hellos every 5 seconds on LAN interfaces and every 60 seconds on WAN interfaces; the hold timer is three times the hello timer (15 or 180 seconds, respectively).
OSPF: By default, OSPF uses a 10-second Hello timer and 40-second Hold timer on broadcast and point-to-point links, and a 30-second Hello timer and 120-second Hold timer for all other network types.
IS-IS: By default, IS-IS uses a 10-second hello interval and 30-second dead interval, with the exception of a broadcast segment’s designated router, which sends hellos at one-third the normal interval (every 3.3 seconds).[6]

13. What is an IS-IS overload bit?
When an overload-bit is set on a particular router, it signals other routers in the network topology not to use it as transit router while sending any of data traffic. The value of overload-bit is 1 if set and 0 if not set.
14. Difference between IPV4 and VPNV4 prefixes
When an RD is added to an IPV4 prefix, then it becomes a VPNV4 prefix. VPNV4 address is total of 96 bit, i.e. 32 bits IP address and 64 bits RD. Simple BGP cannot transport this prefix and a different flavour of BGP i.e. MP-BGP is used to carry VPN4 prefixes in MPLS backbone.
15. Difference between LDP and RSVP
LDP:
- Label Distribution Protocol used for dynamic signaling of MPLS LSP.
- LDP does not support TE and follow the IGP path for signaling LSPs.
- LDP associates a set of destination prefixes (FEC) with each LSP.
- LDP is simple to configure and provide full mesh LSPs.
RSVP:
- RSVP is also used by MPLS for dynamic signaling of LSPs.
- It was actually designed and used as Resource Reservation protocol for Internet.
- RR is an important aspect of Traffic Engineering. For the same reason, RSVP was extended (EROs, Label Distribution) to be used with MPLS for TE purposes.
- RSVP does not follow IGP path as it uses EROs and Administrative groups to establish end to end path through the network independent of IGP.[7]
16. What is a Forwarding Equivalence Class (FEC)?
FEC is a group of IP packets which are forwarded in the same manner, over the same path and with the same forwarding treatment.
An FEC might correspond to a destination IP subnet, but it also might correspond to any traffic class that the Edge−LSR considers significant. For example, all traffic with a certain value of IP precedence might constitute a FEC.[8]
17. Difference Between Route Distinguishers and Route Targets
The Route Distinguisher is used to keep all prefixes in the BGP table unique and the Route Target is used to transfer routes between VRF’s/VPNS. The purpose of RD is to ensure that routes are unique in that particular VPN and Route Target then helps in sorting out routes in the appropriate routing table.
The router imports the RT that the other router exports, this does not have to match the RD.[9]
18. BGP Path Selection Algorithm
- Only look at synchronised routes with a valid next hop
- Prefer the highest WEIGHT (Cisco only)
- Prefer the highest LOCAL PREF
- Prefer the route originated by the local router.
- Prefer the shortest AS_PATH
- Prefer IGP Origin code over EGP and furthermore over Incomplete
- Prefer the lowest MED
- Prefer EBGP path rather than IBGP path
- Prefer the path through the closest IGP neighbour
- Prefer the oldest EBGP path
- Prefer the path with the lowest BGP router ID.[10]
Weight, Local preference: Applied inwards, significant for outbound traffic
MED, AS-Path: Applied outwards, significant for inbound traffic.
19. BGP Path Attributes
- Well-known Mandatory attributes: These attributes must be included in updates propagated to all peers.
Examples: ASPATH, NEXT-HOP and ORIGIN
- Well-known Discretionary attributes: Optional Attributes to include in updates.
Examples: LOCAL_PREF & ATOMIC_AGGREGATE
- Optional Transitive attributes: Should be accepted by BGP Peers even if that attribute is not supported by that router.
Examples: AGGREGATOR and COMMUNITY
- Optional Non-transitive attribute: Non-transitive means that if the BGP router does not recognize the attribute, it can ignore it and not pass it on.
Examples: MED, Originator ID and Cluster List.
20. Explain BGP Synchronization rule
The rule says, “Do not use a route obtained via IBGP unless you have route to the same network via IGP.”
As we know all IBGP neighbours should be fully meshed and as per split horizon rule, no iBGP learned route will be advertised to another iBGP peer unless all of the routers within the AS have learned about the route via an IGP. So, this rule will be enforced whenever you’ll try to make a non-fully-meshed iBGP topology work.
21. Explain the Loop Prevention mechanism in BGP
BGP uses TCP port 179 and BGP Loop prevention is done with the help of AS Number.
When BGP updates travel through different Autonomous Systems (AS), EBGP routers prepend their AS to AS PATH attribute. BGP routers use this information to check through which Autonomous Systems certain updates passed. If an EBGP speaking router detects its own AS in AS_PATH attribute update, the router will ignore the update and will not advertise it further to IBGP neighbors, because it is a routing information loop. This is a built in mechanism for loop prevention in BGP.[11]
22. Difference between IntServ and DiffServ Model
In the Integrated Service model, the application program applies to the network for specific service, and does not send packets until the arrival of confirmation that the network has reserved resources for it.
In the Differentiated Service model, the application program does not need to send its request for network resources before sending packets. Instead, the application program notifies network nodes of its QoS requirements by setting QoS parameters in the IP header.
23. Difference between WFQ, CBWFQ and LLQ
WFQ: WFQ uses an intelligent congestion management solution that provides “fair” sharing of the interface bandwidth between multiple traffic flows.
It is a flow-based queuing algorithm that is doing two things in parallel:It is scheduling interactive traffic to the front of the queue (to reduce response time) and it is fairly sharing the remaining bandwidth between other high bandwidth flow.
CBWFQ: It allows creation of user-defined classes (with the help of flexible class-maps(unlike access-lists in WFQ), each of which is assigned to its own queue. Each queue receives a user-defined (minimum) bandwidth guarantee, but it can use more bandwidth if it is available.
LLQ: Neither WFQ nor CBWFQ can provide guaranteed bandwidth and low-delay guarantee to selected applications such as VoIP, that is because those queuing models have no priority queue.
LLQ includes a strict-priority queue (and is otherwise similar to CBWFQ),that is given priority over other queues, which makes it ideal for delay and jitter-sensitive applications.
24. Difference between RED and WRED
RED Scheme is an Active Queue Management Scheme, which can sense congestion before its occurrence and can take appropriate preventive action.
RED uses a traffic profile to determine the packet-dropping strategy based on the average queue length.
Issue with RED is that cannot differentiate between traffic types so WRED comes into picture. Here, the probability of dropping packets is based not only on the size of the queue but also on the traffic flow type (IP precedence/DSCP values etc).
WRED drops less important packets more aggressively than more important packets (depending upon the flow type).
25. Difference between Transport and Tunnel modes in IPSEC VPNs
Tunnel Mode:
- Tunnel mode protects the internal routing information by encrypting the IP header of the original packet. The original packet is encapsulated by a another set of IP headers.
- It is widely implemented in site-to-site VPN scenarios.
- NAT traversal is supported with the tunnel mode.
- Additional headers are added to the packet; so the payload MSS is less.
- A new IP header is created in place of the original; this allows for encryption of the entire original packet.
Transport Mode:
- The transport mode encrypts only the payload and IP header of the original packet is not encrypted.IP Header can be auhtenticated but not encrypted
- The IPsec Transport mode is implemented for client-to-site VPN scenarios.
- NAT traversal is not supported with the transport mode.
- MSS is higher, when compared to Tunnel mode, as no additional headers are required.
- The transport mode is usually used when another tunneling protocol (such as GRE, L2TP) is used to first encapsulate the IP data packet, then IPsec is used to protect the GRE/L2TP tunnel packets.[12]
26. Different types of LSP protections
There are two different ways to provide LSP protection:
- One-to-One Protection / Detour: An individual backup path is fully signaled through RSVP for every LSP, at every point where protection is provided (i.e. every node). The label depth remains at 1, but this can involve a huge number of reservations, and can cause significant overhead.
- Many-to-One Protection / Facility Backup: A single bypass LSP is created between two nodes to be protected. During a failure, multiple LSPs are rerouted over the bypass LSP. Also, different types of failures that can be protected against.
Link Protection and Node protection
- Link Protection / Next-Hop Backup: A bypass LSP is created for every possible link failure.
- Node Protection / Next-Next-Hop Backup: A bypass LSP is created for every possible node (router) failure.
27. Inter-AS MPLS – Difference between Options A, B and C
Option A:
- Back to Back VRF Exchange
- Sort of PE-CE although in actual it is PE-PE. Providers are treating each others as customers.
- SP dont need to exchange internal routing information.
- RT and RD are locally significant
- SP control their own import and export policies
Option B:
- VPNV4 EBGP exchange from ASBR to ASBR
- VPNV4 exchange labels.
- LSP is end to end.
- SPs don’t need to exchange IGP routes
- RT and RD have global significance.
Option C:
- Multihop VPNV4 EBGP exchange.Non connected SP PEs and RR peers VPN4 EBGP peers
- Most scalable but most difficult to implement.
- IPV4 BGP exchange lables at SP edge.
- Implies SP must share internal routing information.
- Local PEs must have IGP routes for remote PEs.
- LSP is end to end
- Possibly exposes Core Routers to internet.[13]
28. Difference between BGP Route Reflectors and Confederations
The main purpose of route reflectors and confederations is to avoid the need to have all iBGP routers fully meshed (fully peered in BGP).
The route reflector design is usually preferred to confederations.
Route Reflectors:
RR prevents the need to have an IBGP full mesh. Moreover, configuration is done only on the router that you intend act like a RR. All other routers are configured as RR-Clients on the RR. No configuration needed on the other routers.
Instead of establishing an IBGP peering with each and every router of the internal BGP mesh, routers establish IBGP sessions with route reflectors only. RRs represent a focal point for IBGP sessions, and form a cluster together with its clients, that is, other routers within an internal BGP mesh.
Confederations:
Confederations are usually used in huge autonomous systems. Basically all you are doing is splitting up your AS into small AS’s.
For example you have AS 100 consisting of 50 routers. You can split it up into any number of small AS’s, let us say 10 with each containing only 5 routers. These 10 AS’s would then be known as confederations. iBGP speakers in sub-AS are fully meshed.
You can use route-reflectors with confederation sub-AS to reduce the sub-AS iBGP mesh.
29. How does a Route Reflector work?
When an RR receives a route update from its iBGP peers, it selects the best path and follows one of the following rules depending on the type of peer that sent the route:
- EBGP Peer: The best routes are propagated to all BGP peers including other RRs, client peers, and non-client peers.
- Non-client Peer: The best routes are reflected to all the client peers as well as to the eBGP peers.
- Client Peer: The best routes are reflected to all non-client peers as well as to the client peers.
The internal peers that connect to an RR are classified as RR client peers. Every other iBGP router that is not an RR or an RR client is classified as a non-client peer.[14]
References:
[1]. https://www.juniper.net/documentation/en_US/junos/topics/concept/qinq-tunneling-ex-series.html
[2]. https://forums.juniper.net/t5/Junos/difference-Draft-Martini-and-Kompella/td-p/1233
[3]. https://www.cisco.com/c/en/us/td/docs/ios/12_2sb/feature/guide/gigeth.html
[4]. https://learningnetwork.cisco.com/thread/8949
[5]. https://www.juniper.net/documentation/en_US/junos/topics/concept/is-is-routing-overview.html
[6]. http://packetlife.net/blog/2008/may/14/hello-timer-behaviors/
[7]. https://forums.juniper.net/t5/Routing/MPLS-Based-SPF-amp-TE-Solutions-LDP-RSVP-TE-amp-Segment-Routing/ta-p/445271
[9]. http://packetlife.net/blog/2013/jun/10/route-distinguishers-and-route-targets/
[10]. https://www.cisco.com/c/en/us/support/docs/ip/border-gateway-protocol-bgp/13753-25.html
[11]. http://www.getnetworking.net/bgp/bgp-loop-prevention
[12]. https://kb.juniper.net/InfoCenter/index?page=content&id=KB5302
[13]. http://uruhu.su/doc/Cisco_I-AS-MPLS.pdf
[14]. https://www.packetdesign.com/blog/what-is-a-bgp-route-reflector/
Ahmed Zeeshan
Latest posts by Ahmed Zeeshan (see all)
- How I Cracked My CISSP? - July 21, 2023
- Amazon Web Services (AWS) – The Market Leader - August 2, 2020
- My Journey to Huawei HCIE 🙂 - March 15, 2020

Hi,
Brother thanks for the feedback. I can understand what you are saying and to agree to it to some extent hwoever in my opinion one need to know the basics and also you need to know the variety of questions which can be asked in interviews and areas which can be touched during interviews
Good article, but I think question examples are a bit too theoretical. They’re good topics, but good interviewers will form the questions to be more practical or scenario-based, so that you need to apply your knowledge rather than just recite it. For example like in some of these Network Engineer interview questions: https://www.testdome.com/d/network-administrator-interview-questions/120
This post is really helpful and please provide some more interview questions on networking.
Thank you, Krishna.
Please provide the more questions related to networking and this sheet is awesome I learned a lot
Thanks, Piyush. Glad that it helped 🙂